One of the top challenges facing enterprise owners is ensuring secure remote connections to company networks and resources to stay safe from data breaches. In a recent IBM report, the average cost of a data breach in 2024 was estimated at $4.88 million — which IBM says is the highest total ever recorded. With this, it isn’t a surprise that deploying enterprise-level virtual private network solutions has become a top priority for many businesses.
Enterprise VPN solutions provide a secure gateway for businesses to connect their employees to their corporate networks. Security features such as multi-factor authentication, disabling split tunneling, implementing a maximum connection-time window after which employees must re-authenticate, and mandating complex, rotating passwords are several examples of how enterprise VPNs improve and bolster security.
Given the wide range of VPNs on the market, here is a roundup of the top enterprise VPN solutions.
Top enterprise VPN solutions comparison
The table below highlights some of the key features of enterprise VPN solutions and how they compare with one another.
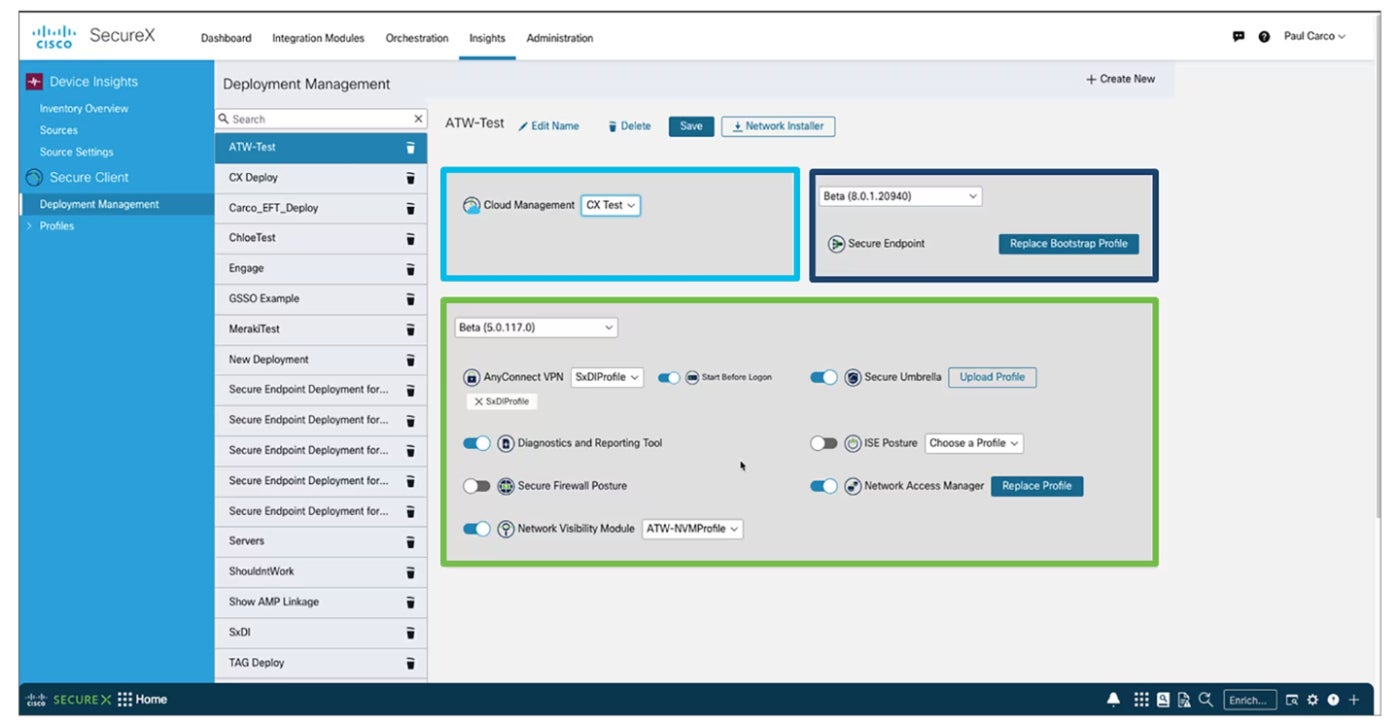
Cisco AnyConnect: Best overall
Cisco AnyConnect is my best overall pick for its wide range of security capabilities, quality customer support, and user-friendly experience. It uses multi-factor authentication and establishes a 24-hour usage window, after which a user’s connection drops and they are required to log in again.
SEE: Can a VPN Be Hacked? (TechRepublic)
A highlight for me is how it performs a system check on authentication to determine whether a workstation meets certain requirements, like anti-malware software or corporate domain membership, before it permits access to the company network. This ensures only company-managed systems are allowed on the VPN. I also like how AnyConnect can block access to untrusted servers, display security products installed, and run diagnostics to gather information for analysis and troubleshooting. It disables split tunneling, meaning when a user is connected to the VPN, they can only access corporate resources and nothing on a local home network or the internet.
Why I chose Cisco AnyConnect
I picked Cisco AnyConnect for its user-friendly installation process and intuitive interface. I also find great value in its suite of security features, such as system check and server blocking, that make it a strong option amongst other enterprise VPN solutions with more limited capabilities. Per my research, it also gets glowing reviews from users in terms of its stability and overall reliability.
Pricing
- Contact the vendor for pricing details.
Features
- Allows access to the enterprise network, from any device, at any time, in any location.
- Provides visibility and insight into endpoint behavior.
- Offers multi-factor authentication.
- Offers always-on support.
Pros and cons
| Pros | Cons |
|---|---|
| It is easy to download and install. | There is no free trial. |
| It can be used on multiple devices. | Lacks kill switch capability. |
| Provides great customer support. |
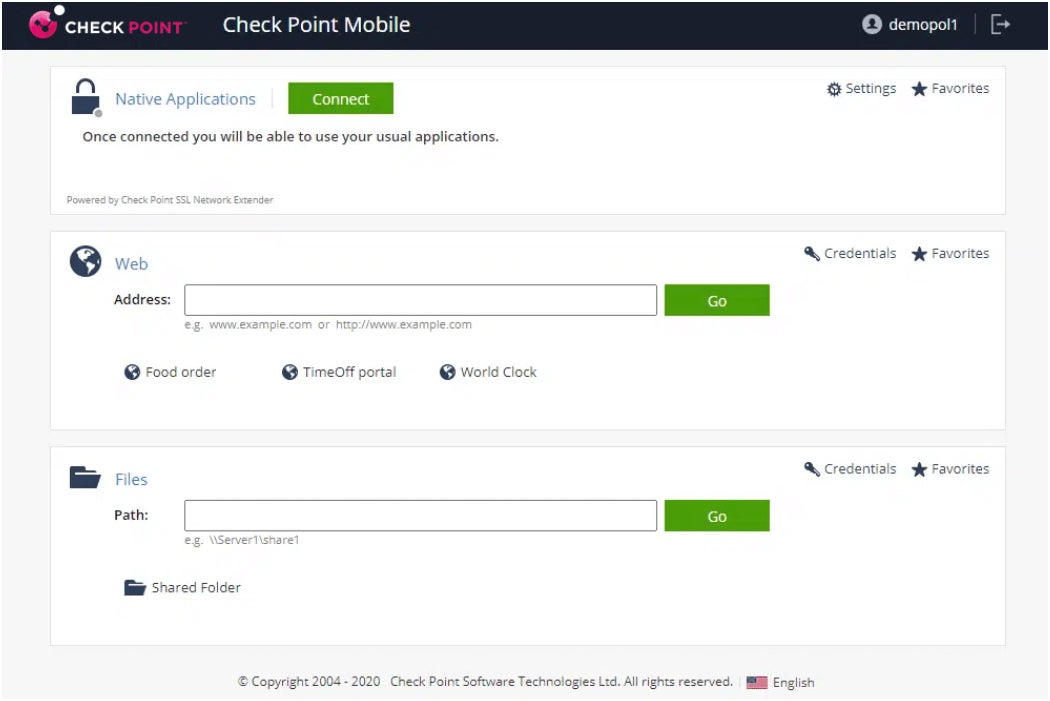
Checkpoint Secure Remote Access: Best for web-based client support

For quality web client support, I recommend Checkpoint Secure Remote Access VPN. It can create custom install packages pre-configured with the target IP address(es) for clients to authenticate to. Like AnyConnect, it’s secured by multi-factor authentication (in this case, either hard tokens or soft tokens, which operate as an app on mobile devices).
SEE: How Much Does a VPN Cost? + Savings Tips (TechRepublic)
I personally like how split tunneling is disabled in Checkpoint Secure Remote Access, just like Cisco AnyConnect. This means, for hackers to get to the clients, they would have to configure the company proxy server settings, which only permit access to public-facing internet sites for business use (social media sites were blocked, for instance). Group memberships determine who can connect where. Checkpoint firewalls serve as the management interface for both the VPN and the firewall settings.
I also want to mention that Checkpoint Site-to-Site VPNs are able to link two remote areas together — allowing traffic to reach networks on either side.
Why I chose Checkpoint Secure Remote Access
I have Checkpoint Secure Remote Access VPN on this list for its impressive SSL VPN portal that allows network access through a web browser. Having secure access to a corporate network is a meaningful value-add that many employees and employers will find useful, especially those working in a hybrid setup. I also feel it makes workflows more efficient, since employees can access important resources without having to install a full-fledged VPN client on their devices.
Pricing
- Contact the vendor for pricing details.
Features
- The VPN offers a central management platform.
- IPsec and SSL VPN support.
- Secure hotspot registration.
- It offers VPN auto-connect.
- Multi-factor authentication support.
Pros and cons
| Pros | Cons |
|---|---|
| SSL support provides web-based access without the need to install a VPN client. | It does not support threat prevention on iOS, Android, and Linux users. |
| Compliance scanning support. | Incident analysis is only available for Windows users. |
| Runs on multiple devices, including Windows, Mac, and mobiles. | |
| Offers threat prevention capability. |
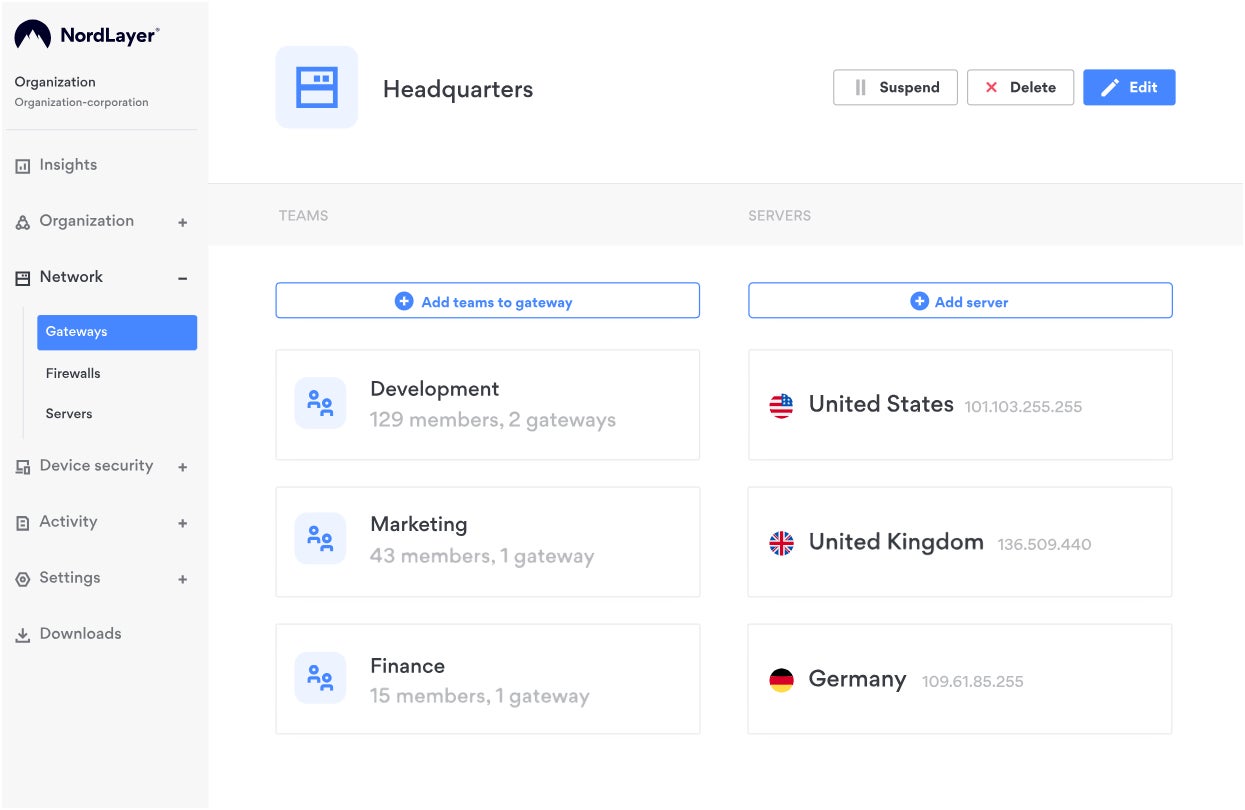
NordLayer: Best for new enterprise VPN users

For businesses transitioning to an enterprise VPN solution, I recommend NordLayer. It’s a powerful remote access solution that enables businesses to secure their remote employees and protect company resources at the same time. If it sounds familiar, it’s because it’s from the same company that created the popular consumer VPN — NordVPN.
Like NordVPN, I like how NordLayer offers an extensive suite of security features without sacrificing ease of use. Some of its features include smart remote access, Always On VPN, Custom DNS, and DNS filtering by category. One big advantage I found with NordLayer is its transparency with pricing, providing estimated prices depending on your needs or subscription of choice. To me, this is an underrated feature that’s perfect for prospective enterprise VPN users.
Why I chose NordLayer
I chose NordLayer for its strong emphasis on ease of deployment, installation, and scalability — which is ideal for businesses that want to start using an enterprise VPN. This allows NordLayer to accommodate most, if not all, business sizes without much headache. I also like that it offers its own proprietary NordLynx protocol, based on WireGuard, that’s built for both speed and security.
Pricing
NordLayer has a monthly and a yearly option for its four subscription tiers. Below is a quick rundown of its annual pricing.
- Lite: $8 per user, per month; 5 users minimum; essential internet access security with basic internet threat prevention.
- Core: $11 per user, per month; 5 users minimum; advanced access security, and basic network access control.
- Premium: $14 per user, per month; 5 users minimum; network access control solutions with granular network segmentation.
- Enterprise: $7 per user, per month; 50 users minimum; custom-fit network security.
Features
- Device posture security.
- MFA and SSO.
- Always On VPN.
- Activity monitoring reports.
Pros and cons
| Pros | Cons |
|---|---|
| Subscription tiers that cater to various enterprise sizes. | Fairly new to enterprise VPN space. |
| Highly scalable. | |
| Publicly available pricing. |
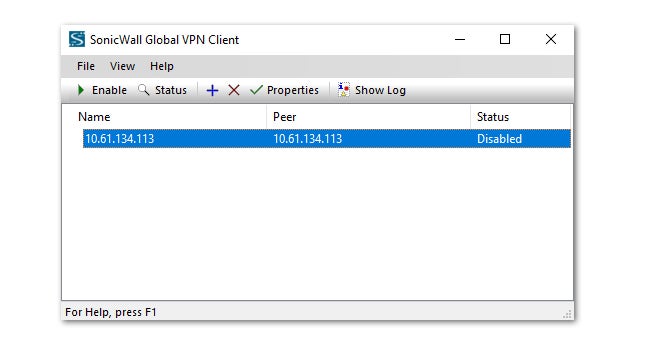
SonicWall Global VPN Client: Best lightweight enterprise VPN

For businesses looking for a lightweight option, I suggest SonicWall Global VPN. It offers a fast and efficient product that provides RADIUS/certificate/Smart Card/USB authentication. It comes with both 168-bit key 3DES (Data Encryption Standard) and AES (Advanced Encryption) encryption standards and VPN session reliability that redirects clients to other VPN gateways if problems occur. I particularly appreciate how SonicWall comes with specific subnet access and command-line options for installation, making it easy to deploy through automated software mechanisms.
Why I chose SonicWall Global VPN Client:
I selected SonicWall Global VPN to be on this list for its speed and reliability. It has a good mix of strong security features, such as AES encryption, an easily configurable interface, and a quick and reliable user experience. SonicWall also has a good reputation for providing quality customer support.
Pricing
- Contact the vendor for pricing details.
Features
- It can be configured either as an IPsec or SSL end-point agent.
- Supports multiple platforms, including Windows, macOS, and Linux.
- Offers easy setup and configuration.
- Detailed logs and reporting for network administrators.
Pros and cons
| Pros | Cons |
|---|---|
| Offers strong encryption and authentication to protect against cyber threats. | There is no free trial or demo. |
| It is easy to download and configure. | No web-based version. |
| Compatible with a wide range of platforms and devices. | |
| Offers logs and reporting features to monitor VPN usage. |
Fortinet FortiClient: Best for offering wider VPN security options

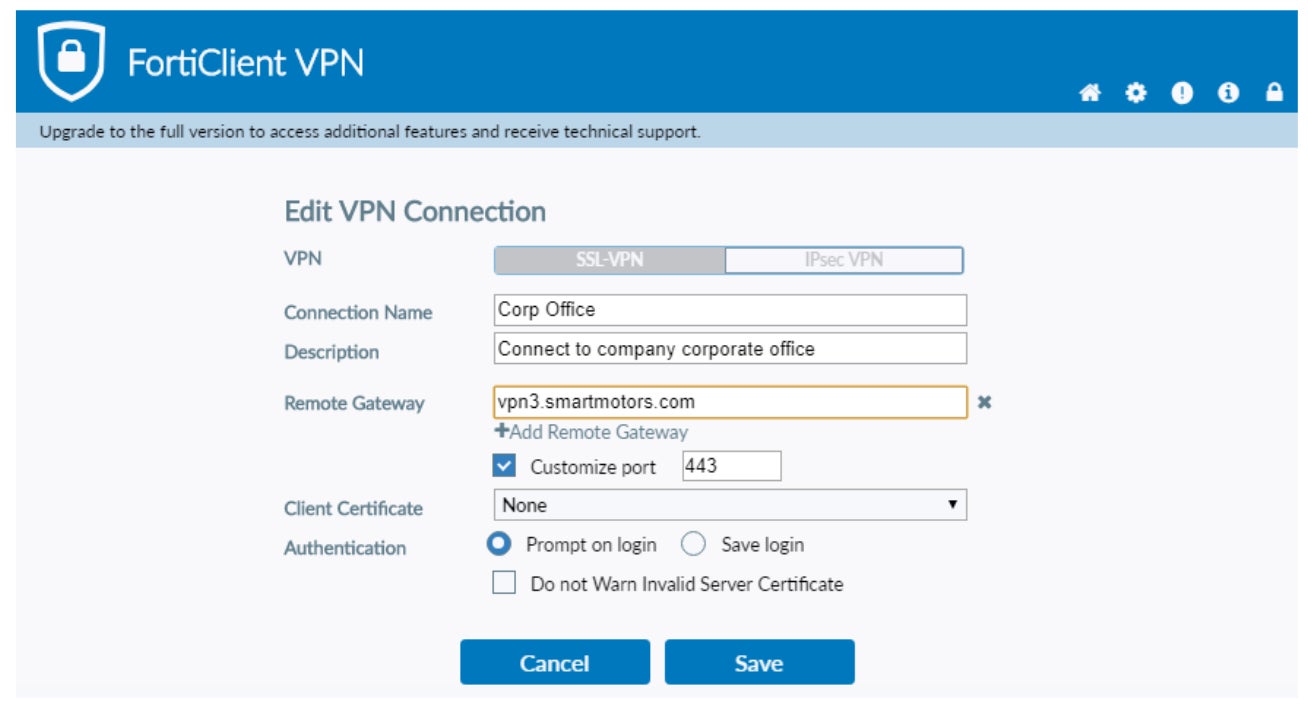
For businesses looking to have flexibility in terms of VPN security options, I recommend Fortinet FortiClient. It relies on certificates for integration and deployment and offers access to web filtering and a firewall. I also like how its Endpoint protection security capabilities, which uses automated behavior analysis, is included. Fortinet utilizes a “single pane of glass” approach that provides one-stop-shopping to manage configuration, deployment, and management, as well as check client status and engage in vulnerability scanning and patching.
I appreciate how Fortinet offers two different types of VPN solutions — IPSec and SSL — and can be integrated into an organization’s overall endpoint security strategy. This provides a reliable VPN security option for companies that have employees working remotely.
Why I chose Fortinet FortiClient
I chose Fortinet FortiClient for its extensive protocol suite, making it a good choice when security is a top priority. It also stood out for me due to its wide variety of tunneling protocols that are customizable based on protection needs. I also like that Fortinet allows prospective users to trial FortiClient to see if it fits their enterprise needs.
Pricing
- Contact the vendor for pricing details.
Features
- Fortinet supports multi-factor authentication.
- Supports SSL or IPSec tunneling protocols.
- Offers malware protection and anti-exploit support.
- Offers multiple tunneling protocols, including Point-to-Point, Layer 2, and Secure Socket tunneling protocols.
Pros and cons
| Pros | Cons |
|---|---|
| There is a free trial option. | Integration with anti-virus and threat-detection tools makes it a little bit clunky. |
| Fully customizable authentication settings. |
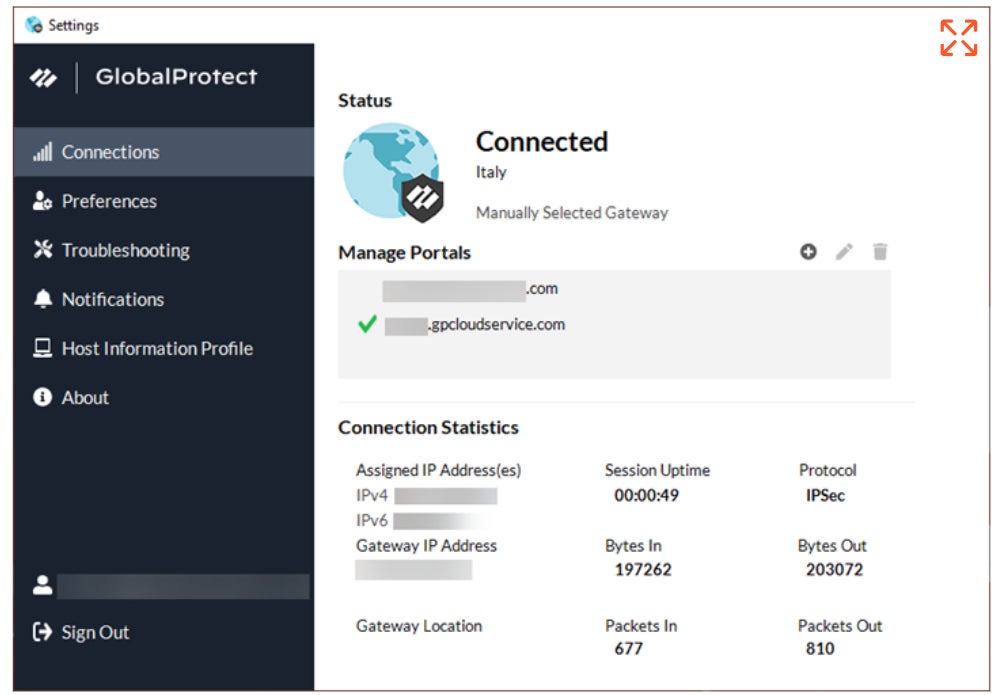
Palo Alto GlobalProtect: Best for implementing security policies

For enterprises that want a VPN with reliable security policy capabilities, I suggest looking into Palo Alto GlobalProtect. It offers similar features to prior products listed, such as multi-factor authentication, high security (cookie or certificate-based authentication are two strong features), web filtering and threat protection. In addition, GlobalProtect relies on Zero Trust principles.
Personally, I commend GlobalProtect’s impressive ability to identify what devices are connecting to the VPN and whether they are managed (company-owned or operated) or unmanaged (employee-owned), and providing access accordingly (devices deemed suspicious or unauthorized can be blocked entirely). It can also determine certificates present on devices, operating system and patch levels, anti-malware versions and status, running software, and whether disks are encrypted and data is being backed up by a product.
Why I chose Palo Alto GlobalProtect
I opted for Palo Alto GlobalProtect due to its trustworthiness and reliability in upholding its security policies and feature promises to its clients. Trust and credibility are important tenets in quality security software, and GlobalProtect has continued to maintain a good reputation for protecting corporate and user data. I also find its strong application of zero trust security principles as a meaningful advantage against similar competitors.
Pricing
- Contact the vendor for pricing details.
Features
- Provides least-privilege access support for remote employees.
- Supports multi-factor authentication.
- The software supports threat prevention.
- Offers full visibility across all applications, ports, and protocols.
Pros and cons
| Pros | Cons |
|---|---|
| There is a demo option to check out the product. | Deployment may be difficult for first-time users. |
| Offers analytics and visibility for network traffic, | |
| There is an always-on, secure connection support. |
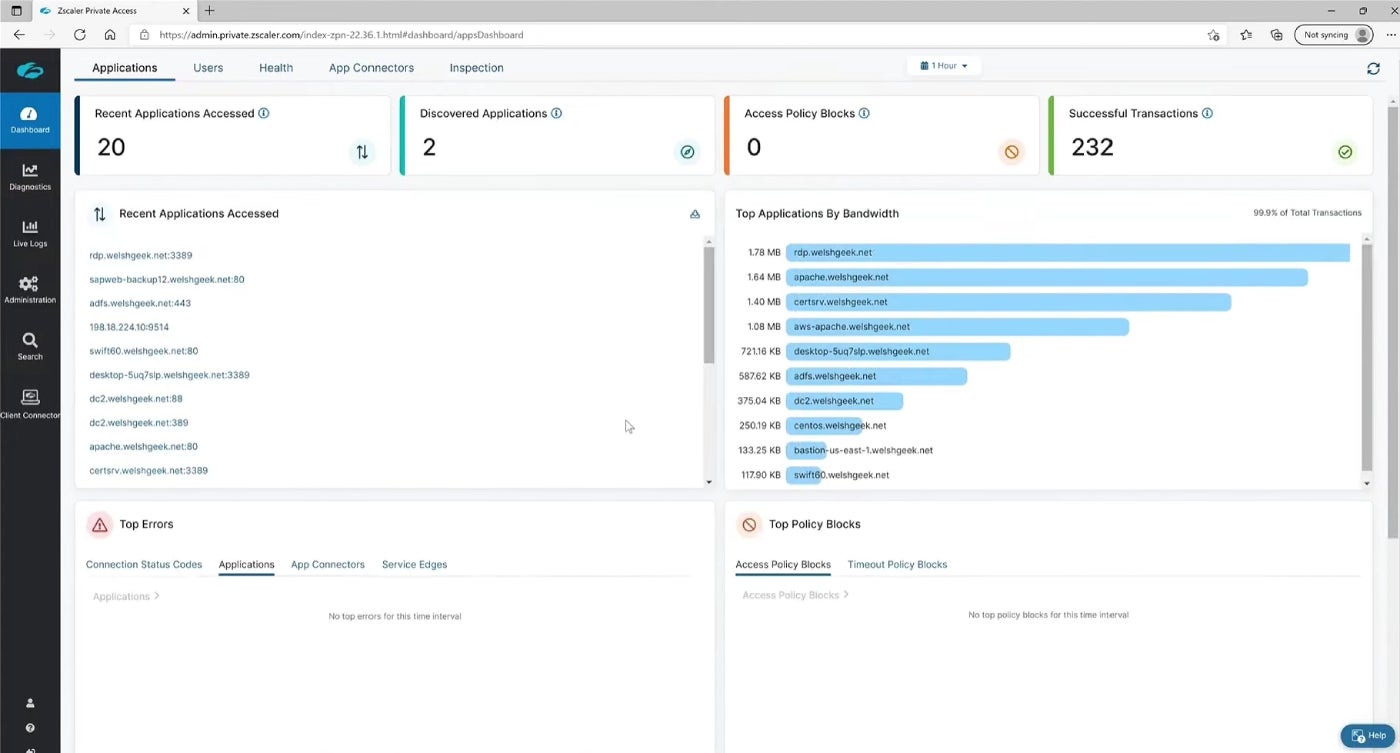
ZScaler Private Access: Best for zero trust network access

If you’re looking for a ZTNA solution, I recommend ZScaler Private Access. As a disclaimer, Zscaler is a different product from the previous offerings in this article. Rather than being a traditional end-user VPN client, it’s a cloud service that provides access to applications in cloud environments or on-premises systems via a distributed architecture. The twist here is that the applications connect to authorized users via secure encryption rather than vice versa, so users never actually access the remote networks involved.
It uses standard policy-based access, depending on users and applications. For me, I like how ZScaler enables mergers and acquisitions to be facilitated easily due to the reduced infrastructure setup times and lack of need for additional networking equipment.
Why I chose ZScaler Private Access
I have ZScaler Private Access on this list for its zero trust approach that can provide organizations peace-of-mind in an increasingly hybrid workforce. While it isn’t a VPN per se, I feel its cloud service adopts maximum security in protecting corporate data and adds an additional layer of security against possible data breaches.
Pricing
- Contact the vendor for pricing details.
Features
- Multiple device support.
- Provides multi-factor authentication.
- AI-powered network segmentation.
- Supports different types of segmentations, including user-to-app, user-to-device, and workload-to-workload segmentation.
Pros and cons
| Pros | Cons |
|---|---|
| There is an option for a demo. | It is only cloud-based. |
| Applies the principles of least privilege to give users a secure connection. | |
| There is security compliance support. |
Key features of enterprise VPN solutions
Enterprise VPNs have key features that separate them from the traditional consumer VPNs. Below are some of the differentiating factors.
Support for Secure VPN Protocol
Support for secure VPN protocols is a crucial feature of enterprise VPNs. These protocols are designed to ensure the confidentiality, integrity, and authenticity of data transmitted between remote users and the corporate network. Enterprise VPNs typically support multiple secure protocols, such as OpenVPN, IPSec, and SSL/TLS, to provide a variety of options for connecting to the network securely. The use of secure VPN protocols help protect sensitive information from interception, eavesdropping, and other types of cyber threats.
SEE: How to Run a Cybersecurity Risk Assessment in 5 Steps (TechRepublic Premium)
DNS Leak Protection support
DNS leaks can compromise the security of enterprise networks by exposing employees’ online activities and potentially allowing unauthorized access to sensitive company data. Enterprise VPN solutions need robust, built-in DNS leak protection mechanisms to ensure that all DNS queries are routed through the encrypted VPN tunnel and not leaked outside.
Centralized management support
A centralized management system allows administrators to quickly and easily configure VPN settings and policies, monitor VPN traffic and usage, and troubleshoot network issues. With a centralized management network, admins can also enforce policies — such as access controls and data retention policies, across the entire VPN network — ensuring that all users comply with company security policies and industry regulations.
High availability
High availability is another critical feature of enterprise VPNs. Having an enterprise VPN consistently and continuously operate properly is a crucial feature to watch out for. Any downtime in an enterprise VPN’s performance can disrupt business operations, preventing remote workers from accessing corporate resources and potentially causing revenue losses.
How do I choose the best VPN solution for my business?
Before opting for any VPN software for your business, I recommend you take time to consider the following:
Consider your business security needs
First, consider your security needs and check if your potential VPN solution can meet those needs. For instance, if your security need goes beyond just a secure VPN connection to include, let’s say, compliance support, you should go for a VPN solution that offers both. Similarly, you should also consider how you want to deploy your VPN software. Do you want a solution offering only a cloud-based or downloaded client? Your answer will allow you to pick the best VPN software for your business.
Consider security capabilities
While all VPN solutions offer similar security capabilities, some have more security-focused features than others. Remember that security should be the top priority when choosing an enterprise VPN solution. You should go for solutions that provide strong encryption, secure authentication, and other security features to protect against cyber threats.
Check for compatibility
Compatibility is another factor to consider before opting for any business VPN solution. The VPN solution should be compatible with a wide range of platforms and devices, including desktops, laptops, mobile devices, and different operating systems. This ensures that your employees’ devices can easily connect to the VPN without spending money on additional devices.
Consider cost
Consider the cost of the VPN solution, including any hardware or software licenses, maintenance and support fees, and any other expenses associated with implementation and management.
Methodology
While there are several VPN services out there, not all offer solutions at an enterprise level. To arrive at this list of the best enterprise VPNs, I based our selection on the following parameters: strong security features, stable connection, multi-device and operating system capability, and customer support. Apart from using some of the solutions, I also checked out reviews on Gartner to gather third-party opinions and user testimonials on some of the VPN solutions.
From these aspects, I highlighted the main differentiating feature that makes each specific enterprise VPN worth checking out.
This article was originally written by Scott Matteson and updated by Franklin Okeke. The current version contains additional information and updates by Luis Millares.


